Cara Hack Facebook Dengan Social Engineering Toolkit Mac
Metode hack Facebook pun bermacam-macam jenisnya seperti menggunakan software, dengan fake login, dengan id fb, dan masih banyak lainnya. Kami yakin anda pasti mempunyai akun facebook, untuk itu lebih baik ketahui apa saja cara hack facebook agar akun facebook kita aman dari pembobol.
I love hacking humans. There is a sense of art to operating in the realm of mind tricking. If you are a magician, you may have some feelings of satisfaction when you successfully tricked your audience. You realize people in front of you are fools who are amazed by dumb things.Social Engineering Attacks (from the hacking perspective) is quite similar to performing a magic show. The difference is, in Social Engineering Attacks, its a magic trick where the result is a banking account, social media, email, even access to a target computer. Who created the system? A HUMAN. Doing Social Engineering Attack is easy, trust me, it is really easy. No system is safe. Humans are the best resource and the end-point of security vulnerabilities ever.
In the last article, i did a demo of Google account targeting, Kali Linux: Social Engineering Toolkit, this is another lesson for you.
Do we need certain Penetration Testing OS to do Social Engineering Attack? Actually not, Social Engineering Attack is flexible, the tools, such as Kali Linux are just tools. The main point of Social Engineering Attack is about “designing the attack flow”.
In the last Social Engineering Attack article we learned the Social Engineering Attack using “TRUST”. And in this article we will learn about “ATTENTION”. I got this lesson from a “King of Thieves” Apollo Robbins. His background is skilled magician, street magician. You could see his show on YouTube. He once explained in a TED Talk, about how to steal things. His ability is mainly, playing with the victim’s attention to pickpocket their stuff, such watches, wallet, money, card, anything in the victims’ pocket, without recognition. I will show you how to conduct Social Engineering Attack to hack someone’s Facebook account using “TRUST” and “ATTENTION”. The key with “ATTENTION” is to keep talking fast, and ask questions. You are the pilot of the conversation.
The Social Engineering Attack Scenario
This scenario involves 2 actors, John as an attacker and Bima as a victim. John will set Bima as a target. The goal of Social Engineering Attack here is, to get access to the victim’s Facebook account. The attack flow will use a different approach and method. John and Bima are friends, they often meet in the canteen at lunch time during rest time in the their office. John and Bima are working in different departments, the only occasion they meet is when they have lunch in the canteen. They often meet and talk to each other until now they are mates.
One day, John “bad guy”, is determined to practice Social Engineering Attack using “ATTENTION” game, which i mentioned earlier, he got inspired by “The King of Thieves” Apollo Robbins. In one of his presentations, Robbins said that, we have two eyes, but our brain can only focusing on one thing. We can do multitasking, but its not doing the different tasks together at the same time, instead we just switch our attention to each task quickly.
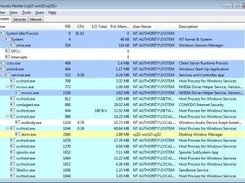
At the beginning of the day, on Monday, in the office, as usual John is in his room siting at his desk. He is planning to get the strategy to hack his friend’s facebook account. He should be ready before lunch. He is thinking and wondering while sitting at his desk.
Then he takes a sheet of paper, sits in his chair, which is facing his computer. He visits Facebook page to find a way to hack someone’s account.
STEP 1 : FIND STARTER WINDOW a.k.a HOLE
On the log on screen, he notice a link named “forgotten account”, Here John will be using the benefit of “forgotten account (password recovery)” feature. Facebook has already served our starter window at: “https://www.facebook.com/login/identify?ctx=recover”.

The page should looks like this:
In the field “Find Your Account” section, there is a sentence which says, “Please enter your email address or phone number to search for your account”. From here we get another set of windows: email address refers to “Email Account” and phone number refers to “Mobile Phone”. So, John has a hypothesis that, if he had the victim’s email account or mobile phone, then he will have access to the victim’s Facebook account.
STEP 2 : FILL IN THE FORM TO IDENTIFY THE ACCOUNT
Okay, from here John starts thinking deeply. He doesn’t know what is Bima’s e-mail address, but he saved Bima phone number on his mobile phone. He then grabs his phone, and looks for Bima’s phone number. And there he goes, he found it. He begins typing Bima’s phone number in that field. After that he presses “Search” button. The image should look like this:
He got it, he found that Bima’s phone number is connected to his Facebook account. From here, he just holds, and does not press the Continue button. For now, he just made sure that this phone number is connected to the victim’s Facebook account, so that comes closer to his hypothesis.
What John actually did, is doing reconnaissance, or Information Gathering on the victim. From here John has enough information, and is ready to execute. But, John will meet Bima in the canteen, it is impossible for John to bring his computer, right? No problem, he has a handy solution, which is his own mobile phone. So, before he meets Bima, he repeats the STEP 1 and 2 on the Chrome browser in his Android mobile phone. It would be look like this:
STEP 3: MEET THE VICTIM
Alright, now everything is set up and ready. All John needs to do is grab Bima’s phone, click the Continue button on his phone, read SMS inbox message sent by Facebook (the reset code) on Bima’s phone, remember it and delete the message in a single fraction of time, quickly.
This plan sticks into his head while he is now walking to the canteen. John put his phone in his pocket. He entered the canteen area, looking for Bima. He turned his head left to right figuring out where the heck is Bima. As usual he is in the corner seat, waving his hand to John, he was ready with his meal.
Immediately John takes a small portion of meal this noon, and comes close to the table with Bima. He says hi to Bima, and then they eat together. While eating, John looks around, he notices Bima’s phone is on the table.
After they finish lunch, they are talking about each others day. As usual, until, then, at one point John open a new topic about phones. John tells him, that John needs a new phone, and John needs his advice about which phone is suited for John. Then he asked about Bima’s phone, he asked everything, the model, the specs, everything. And then John asks him to try his phone, John acts like he is really a customer looking for a phone. John’s left hand grabs his phone with his permission, while his right hand is under the table, preparing to open his own phone. John sets his attention on his left hand, his phone, John talked so much about his phone, its weight, its speed and so on.
Now, John begins the Attack with turning off Bima’s phone ring tone volume to zero, to prevent him from recognizing if a new notification comes in. John’s left hand still has his attention, while his right hand is actually pressing the Continue button. As soon as John pressed the button, the message comes in.
Ding. No sounds. Bima has not recognized the incoming message because the monitor is facing John. John immediately opens the message, reads and remembers the 6 Digit Pin in the SMS, and then deletes it soon. Now he is done with Bima’s phone, John gives Bima’s phone back to him while John’s right hand takes his own phone out and starts typing immediately the 6 Digit Pin he just remembered.
Then John presses Continue. The new page appears, it asked whether he wants to make new password or not.
John will not change the password because he is not evil. But, he now has Bima’s facebook account. And he has succeed with his mission.
As you can see, the scenario seems so simple, but hey, how easily you could grab and borrow your friends’ phone? If you correlate to the hypothesis by having your friends’ phone you can get whatever you want, badly.
- Mobile Tracking
- Mobile Security
- Mobile Spy
Be it personal communications or professional communications, most of them nowadays take place on Facebook. When someone wants to say something, they can just log-in to their Facebook account and spread their message across to all Facebook users. What that means is, if you ever wish to find out information about someone, you can then hack Facebook account of theirs. It will provide you with all information the user has shared on the social media website.
There are multiple ways that let you hack Facebook online using your computer or your other devices. Each of them uses a unique way to help you get access into any user's profile on the Facebook platform. In the following guide, you are going to learn just about that - how to hack Facebook account.
Method 1. The Most Efficient Way to Hack Facebook ID with Spyera
There are tons of spy apps that let you spy on someone's device so you can view their Facebook conversations. However, only a handful of those apps actually work. If you have not found a working app for yourself, the following section will suggest you one.
Enter Spyera, a fully-featured spy app that allows you to spy on anyone's device without them knowing anything about you or the app. Once the app is installed on the victim's device, you can keep an eye on all of their activities that take place on their device.
There are two ways you can use the app to hack someone's Facebook account.
1. Directly Spy on Someone's Facebook Conversations
In this method, you just need to install the app on victim's device and it will begin to send you all of their activities. This doesn't require you to know the username or the password of the victim's Facebook account. Here's how to execute this method:
- Purchase a license for Spyera from its official website.
- Get access to the victim's phone somehow and install the Spyera app on it. You don't need the phone once the app is installed.
- Access your Spyera account and head to Messages > IM > Facebook to view your victim's Facebook account activity.
There you go. That's how you can use the Spyera Facebook hack software to hack into someone's Facebook account.
2. Use Keylogger to Find Out Victim's Login Details
Another option in the Spyera app that allows you to view someone's Facebook data is keylogger. Using the keylogger feature, you can find out what someone's typing including their username and password and you can then use those details to log-in to their Facebook account.
Once you purchase a license for the Spyera app, you will get more information as to how you can install the keylogger and get someone's Facebook login credentials on your device.
Method 2. Hack Facebook Online with Face Geek
If you don't already know, Face Geek is a web based service that allows you to crack passwords of the specified Facebook accounts. It will let you hack into anyone's Facebook account as long as you know the URL of the victim's Facebook account. The following is how you implement this method:
There's nothing else you need to do to hack the account as the tool will take care of the rest for you. It will somehow find out the password of the account and then you can use that password to log-in to your victim's Facebook account.
Method 3. Hack Facebook Password Using Forgot Password Method
You may not be aware of but Facebook has a weakness on it's forgot password page that you can use for your own advantage to hack a Facebook account. What you basically need to do is enter the name of the Facebook account you wish to hack and then click the option that lets you reset a password. You then use the recovery options to get a new password. Here's how to hack Facebook using the forgot password method:
What Facebook will do is send a code to the chosen recovery option and you can use that code to set up a new password for the account. That way, you will gain access to that Facebook account and the owner of the account will lose access as the password has been changed.
Method 4. Hack Facebook Account Using the Phishing Method
Phishing method is a well-known method in the hacking world and it can also be used to hack other accounts such as Google and Yahoo accounts. What you basically need to do in this method is create a login page that looks exactly like the original one and then capture user's login details.
You need to get a hosting account and a domain name. Then, create a fake login page and send the link of that page to your victim. Somehow convince the victim to open the page and enter in his or her login details. The details will then be sent to your email address allowing you to access the victim's Facebook account.
This method uses a bit of social engineering so it helps to have knowledge of that as well.
Conclusion
There may be tons of methods to hack Facebook account but the ones described in this guide actually work and let you get into someone's Facebook account. If you don't want any hassle while hacking the account, Spyera is the way to go.
Diamond VC500 USB 2.0 One Touch VHS to DVD Video Capture Device with Easy to use Software, Convert, Edit and Save to Digital Files $35.47. Easy to Use Capture by the Touch of One Button. Operating System: WIN 10, WIN8, WIN 7 32, WIN 7 64, WIN VISTA32, WINXP, MCE. Diamond usb 2.0 video capture device for mac. Diamond Multimedia VC500MAC USB 2.0 One Touch VHS to DVD Video Capture Device with Easy to use Software, Convert, Edit and Save to Digital Files For MacOS The Diamond One-Touch Video Capture VC500MAC has become the most versatile and easy-to-use device on the desks of many video capture enthusiasts. The VC500MAC comes with RCA and S-Video inputs and also uses a USB 2.0 interface. Any device with a composite output such as a VHS player can be used to transfer video and audio to your Mac or Macbook or Mac based PC. You can also capture and edit video straight from a camcorder and convert them to DVD.
- Remove Apple ID or iCloud account on iPhone/iPad without passwordNEW
- Bypass iPhone/iPad screen passwords instantly
- Fix disabled iPhone/iPad without iTunes or iCloud
- Remove 4-digit/6-digit passcode, Touch ID & Face ID from iPhone/iPad